NoPassword
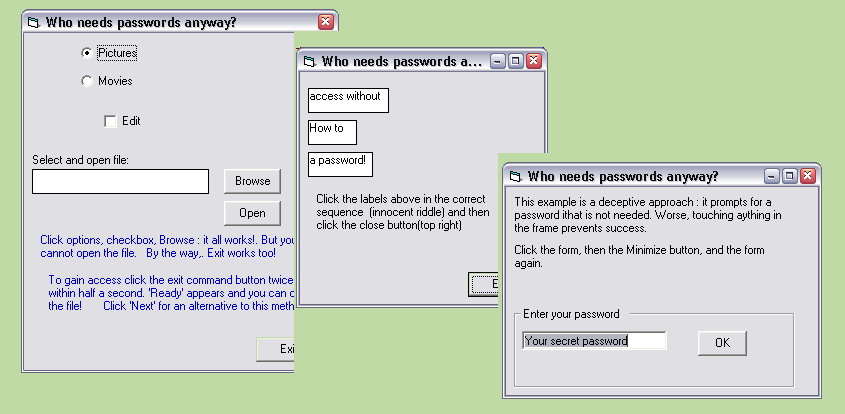
There are other ways than passwords to restrict access to applications. The method I present here is suited for personal and limited public use. You'll see what I mean when you try out the basic method and two alternatives, all nicely packaged in a well commented appliction. But these are just examples. Use your creativity and create your own "protection"-scenario's.
Rate NoPassword
 (7(7 Vote))
(7(7 Vote))
Download NoPassword
Active Server Pages
Coding Standards
Complete Applications
Custom Controls
Data Structures
Databases / ADO
DDE
Debugging & Errors
DirectX
Encryption
Files / I/O
Games
Graphics
Internet / HTML
Jokes / Humor
Libraries
Math / Dates
Office / VBA
Miscellaneous
OOP
OLE / COM / ActiveX
Registry
Sound / MP3
String Manipulation
VB Enhancements
Windows API
Windows CE
System Services